T-Mobile Data Breach Exposes Customers to SIM Swap Fraud

If you were a victim of a T-Mobile hack, call our law firm at 800-767-8040 for a free and confidential case consultation from an attorney. T-Mobile may be liable to you under the Federal Communications Act and the regulations promulgated thereunder.
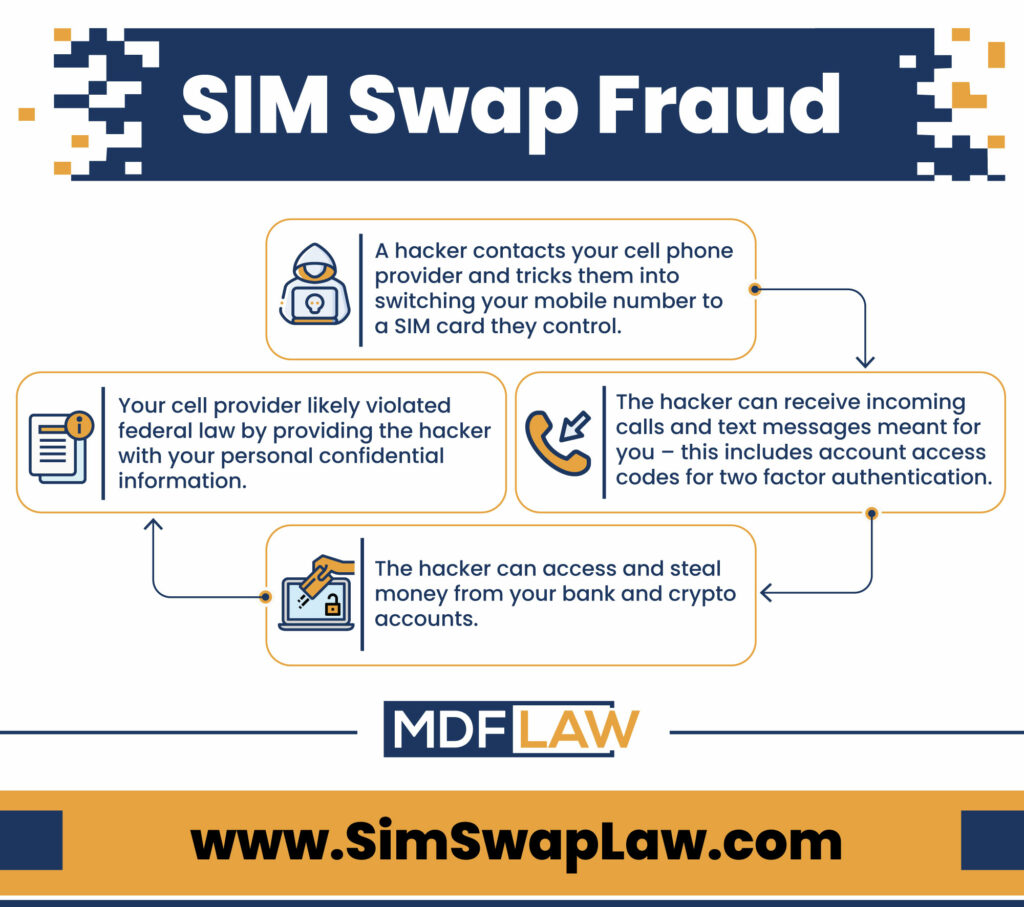
What is SIM Swapping?
SIM Swapping occurs when a criminal takes over a victim’s cell phone to receive an SMS two factor authentication code (2FA). These codes are used to access bank accounts as well as accounts at centralized cryptocurrency exchanges, such as Coinbase. The recent T-Mobile data breach exposes millions of consumers to SIM Swapping attacks.
How Can I Prevent Being SIM Swapped?
To prevent such an attack, we recommend that users do not use cell phones for two factor authentication (2FA) and, instead, use hardware tokens. If you chose to use your cell phone for 2FA, you should contact your mobile carrier and inquire about whether the SIM could be locked or prevented from porting. Using your cell phone as a method of 2FA is not advisable.
Is SIM Swapping Illegal?
Yes, and customers can file a SIM swap lawsuit to recover money damages. T-Mobile, like all cell phone providers, must protect customer’s personal confidential information under the Federal Communications Act, or FCA. Under the FCA, a telecommunications carrier is prohibited from disclosing a customer’s “propriety network information” to unauthorized third-parties. Civil penalties under the FCA include, the “full amount of damages sustained in consequence of any such violation…together with a reasonable counsel or attorney’s fee…” Suing T-Mobile for these damages involves initiating an arbitration and not filing in Court. If you were a victim of SIM swapping, speak to one of our attorneys for a free consultation.
What’s Involved in Suing T-Mobile for SIM Swapping?
Under T-Mobile’s terms of use, customers are required to pursue arbitration and cannot bring claims in Court or file a class action. If you want to discuss filing an arbitration against T-Mobile, please call us at 800-767-8040 to speak with an attorney.
What Information is Needed for a SIM Swap Request by Phone?
A customer must furnish the carrier with a password if a SIM swap request is made over the phone. If a password is not provided, the carrier can only disclose information by sending it to the customer’s address of record or by calling the customer at the phone number of record. You may be able to sue T-Mobile for releasing your SIM information without following these steps.
SIM Swap Fraud Explained
What Information is Needed for a SIM Swap Done in a Store?
If an individual requests a SIM swap at a store, the carrier may only disclose information to an individual who has a valid photo ID, which matches the customer’s account information on file. Suing T-Mobile for releasing your SIM information to an authorized individual at a retail store may involve reviewing security footage from the location as well as other physical evidence.
How Soon After a SIM Swap Must Customers be Notified?
Cell phone providers must notify customers “immediately” whenever there is a change to a password or address or if a customer requests a back-up means of authentication. The provider is required to provide this notification either to the phone number of record (via voice or SMS) or by mail to the address of record. Mobile carriers must also notify both customers as well as federal law enforcement if there is a breach of a customer’s propriety network information, or CPNI.
News Update: January 19, 2023 Data Breach Impacted 37 million Customers
T-Mobile filed a form 8-K with the Securities and Exchange Commission on January 19, 2023, which disclosed a significant data breach, exposing millions of customers’ to T-Mobile SIM swapping attacks. According to the SEC disclosure, hackers first accessed T-Mobile’s system on November 25, 2022, but their activities were not detected until January 5, 2023. The hacking attack leaves many current and former T-Mobile customers exposed to malicious activity, including SIM swapping.
How did T-Mobile’s Recent Data Breach Occur?
According to the disclosure, T-Mobile identified that a malicious actor obtained data from an API, or application programing interface, without permission or authorization. According to T-Mobile, the breach did not expose any customer credit cards, social security numbers or driver’s license information. However, the incident did result in hackers accessing customer’s name, phone number, billing and email addresses and date of birth. The incident impacted 37 million current prepaid and postpaid customers. The filing with the Securities and Exchange Commission warns T-Mobile investors that the company “may incur significant expenses in connection with the incident.”
Were You a Victim of T-Mobile SIM Swapping?
If you or someone you know had an account at T-Mobile and was a victim of T-Mobile SIM swapping, our SIM swap attorneys may be able to assist you. Please call 800-767-8040 or complete the form below for a free and confidential consultation.
