Sim Swap Lawyer: Crypto Theft Can be Traced Back to Sim Card Swap

Sim swap lawyers can help SIM swap victims recover stolen cryptocurrency by suing AT&T, Verizon, T-Mobile, Coinbase, Gemini and Biance. If crypto was stolen because your mobile carrier provided your sim card to someone else – you may be able to sue to recover your losses. Please contact our attorneys at 800-767-8040 for a free and confidential consultation.
Important fact: Your mobile number is not physically stored on the SIM card.
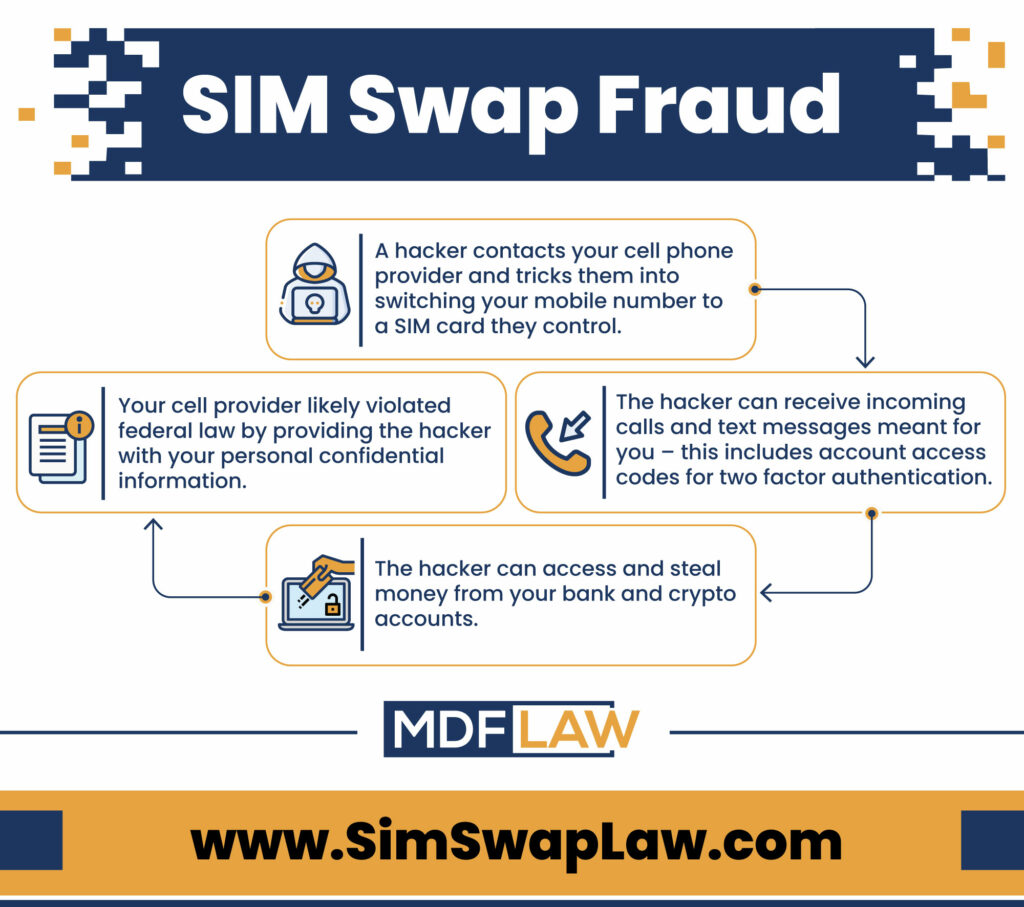
A mobile carrier is like an old-fashioned switchboard. Calls for a certain mobile number come into the operator, and the “switchboard” links the number up with the SIM card’s identity number. Then the “switchboard” sends the call to that SIM, and your phone rings. In a SIM swap scam, fraudsters convince or bribe someone at your mobile carrier to change the SIM card connected to your telephone number. In other words, future calls to that telephone number will be patched through to the fraudster’s SIM card instead of your own.
Once fraudsters have access to your telephone number, they can then use it to change your passwords or gain direct access to numerous online accounts and financial accounts. This is because a very large portion of these accounts sends an authorization code to your telephone either to change the password, or to log in directly.
One of the most disturbing aspects of fraudulent SIM swaps is that they are often carried out entirely without your participation. There are, however, some things you can do to minimize the chances of it happening to you, and also to minimize the potential damage once you recognize that it has occurred.
SIM Swap Lawyer Discusses Sim Swapping
Can you sue your mobile carrier for stolen crypto?
Yes, if your mobile carrier provided your sim card to a fraudster without properly identifying their identify then you may be able to sue them to recover your stolen crypto. These disputes are often handled out of court through binding arbitration pursuant to carrier’s terms and conditions (i.e. “the fine print”). In these arbitration cases, the customer can sue for their lost crypto, attorneys’ fees and lost appreciation. Since ever case is different, however, we encourage you to contact a SIM swap attorney to discuss your specific matter.
How are fraudulent SIM swaps carried out?
A fraudulent SIM card swap must be executed directly on your account by an employee at your mobile network operator. This type of fraud is typically achieved using:
- Social engineering
- Direct bribery (insider threat)
- Phishing
Understanding SIM Swap Fraud
How do you know you have been the victim of a fraudulent SIM swap?
The first sign of a potential SIM Swap on your phone is a “No Service” message. Although this is not necessarily an indication that you’ve been the victim of a SIM swap, you should immediately do the following if you see it:
- Check with any friends or family in the same location if they are also experiencing no service, especially if they use the same provider.
- Contact your mobile operator and ask if a SIM swap has been carried out, then get it rescinded immediately.
- You might have difficulty accessing your online accounts so call your bank and any other financial institutions to place an alert on your account, blocking any suspicious transactions, or even temporarily blocking all activity on the account if that is possible.
How can you protect yourself against a fraudulent SIM swap?
Insider threats aside, the most effective things you can do to prevent fraudulent SIM swaps from happening on your account are:
- Limit the amount of personal data you post online.
- If you are using SMS\Text authentication to gain access to any online accounts, change this to email wherever possible. If the platform does not allow this, seriously consider shifting to another one that does.
- Never reply to any emails asking for information such as your email address, SSN, or any other personally identifiable information.
- If you receive a call asking for PII, do not provide it. The fraudster might be pretending to be calling from your bank. In that case, end the call, go to your bank’s official website, look up their support number, and call them directly. Then ask them if they called and if they require the information the previous caller was requesting. If they didn’t make the call, consider placing an alert on your account while you investigate further.
- Some mobile operators require a PIN to be able to perform a SIM swap. Use a hard-to-guess number or phrase as your PIN. Avoid using birthdays or phrases such as your first name or names of pets. And never post this PIN anywhere online.
Contact a SIM Swap Lawyer
If you had crypto stolen due to a sim card swap, contact our sim swap attorneys today.
